W ramach zabawy i nauki niskopoziomowej zamierzam wstrzyknać dllke do procesu kalkulatora i wyświetlić komunikat. Problem w tym, że wszystko niby przebiegło pomyślnie, kod injectora wykonał się poprawnie, ale dllka się nie wykonała. Proszę o sugestie co mogło pójść nie tak:
DWORD Inject::CreateRemoteThreadW(PCWSTR pszLibFile, DWORD dwProcessId) {
// Calculate the number of bytes needed for the DLL's pathname
DWORD dwSize = (lstrlenW(pszLibFile) + 1) * sizeof(wchar_t);
// Get process handle passing in the process ID
HANDLE hProcess = OpenProcess(
PROCESS_QUERY_INFORMATION |
PROCESS_CREATE_THREAD |
PROCESS_VM_OPERATION |
PROCESS_VM_WRITE,
FALSE, dwProcessId);
if (hProcess == NULL)
{
wprintf(TEXT("[-] Error: Could not open process for PID (%d).\n"), dwProcessId);
return(1);
}
// Allocate space in the remote process for the pathname
LPVOID pszLibFileRemote = (PWSTR)VirtualAllocEx(hProcess, NULL, dwSize, MEM_COMMIT, PAGE_READWRITE);
if (pszLibFileRemote == NULL)
{
wprintf(TEXT("[-] Error: Could not allocate memory inside PID (%d).\n"), dwProcessId);
return(1);
}
// Copy the DLL's pathname to the remote process address space
DWORD n = WriteProcessMemory(hProcess, pszLibFileRemote, (PVOID)pszLibFile, dwSize, NULL);
if (n == 0)
{
wprintf(TEXT("[-] Error: Could not write any bytes into the PID [%d] address space.\n"), dwProcessId);
return(1);
}
// Get the real address of LoadLibraryW in Kernel32.dll
PTHREAD_START_ROUTINE pfnThreadRtn = (PTHREAD_START_ROUTINE)GetProcAddress(GetModuleHandle(TEXT("Kernel32")), "LoadLibraryW");
if (pfnThreadRtn == NULL)
{
wprintf(TEXT("[-] Error: Could not find LoadLibraryA function inside kernel32.dll library.\n"));
return(1);
}
// Create a remote thread that calls LoadLibraryW(DLLPathname)
HANDLE hThread = CreateRemoteThread(hProcess, NULL, 0, pfnThreadRtn, pszLibFileRemote, 0, NULL);
if (hThread == NULL)
{
wprintf(TEXT("[-] Error: Could not create the Remote Thread.\n"));
return(1);
}
else
wprintf(TEXT("[+] Success: DLL injected via CreateRemoteThread().\n"));
// Wait for the remote thread to terminate
WaitForSingleObject(hThread, INFINITE);
// Free the remote memory that contained the DLL's pathname and close Handles
if (pszLibFileRemote != NULL)
VirtualFreeEx(hProcess, pszLibFileRemote, 0, MEM_RELEASE);
if (hThread != NULL)
CloseHandle(hThread);
if (hProcess != NULL)
CloseHandle(hProcess);
return(0);
}
A tutaj kod DLL, prosty jak tylko być może
// dllmain.cpp : Defines the entry point for the DLL application.
#include "pch.h"
#include <iostream>
BOOL APIENTRY DllMain(HMODULE hModule,
DWORD ul_reason_for_call,
LPVOID lpReserved
)
{
switch (ul_reason_for_call)
{
case DLL_PROCESS_ATTACH:
std::cout << "Proc attach\n";
case DLL_THREAD_ATTACH:
std::cout << "Thread attach!\n";
case DLL_THREAD_DETACH:
case DLL_PROCESS_DETACH:
break;
}
std::cout << "Hello World!\n";
return TRUE;
}
#include <iostream>
#include "Inject.h"
#include "SystemInformations.h"
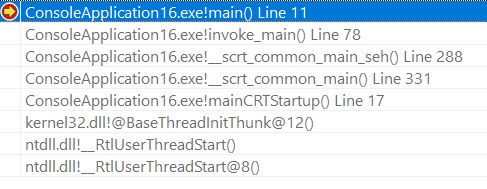
int main()
{
PCWSTR pszLibFile = NULL;
pszLibFile = (wchar_t*)malloc((wcslen(L"sciezka do plika") + 1) * sizeof(wchar_t));
pszLibFile = L"sciezka do plika";
wchar_t x[] = L"Calculator.exe";
wchar_t* point = x;
Inject injection;
SystemInformations sysInfo;
DWORD pid = sysInfo.findPidByName(point);
injection.CreateRemoteThreadW(pszLibFile, pid);
}